Migrate Debuginfo Uploads to Service Accounts
This guide walks you through migrating your CI/CD debuginfo and source upload pipelines from project tokens to the new IAM system using service accounts with minimal role bindings.
What's Changing
Previously, debuginfo uploads authenticated using project-scoped JWT tokens. The new IAM system replaces these with:
- Service accounts — named identities with granular, role-based permissions
- Service account tokens — API tokens (format:
psc_v1_<64-hex-characters>) tied to a service account - Role bindings — assignments that grant only the permissions needed
The project to upload to is now specified separately via a projectID gRPC metadata header, rather than being embedded in the token.
Steps
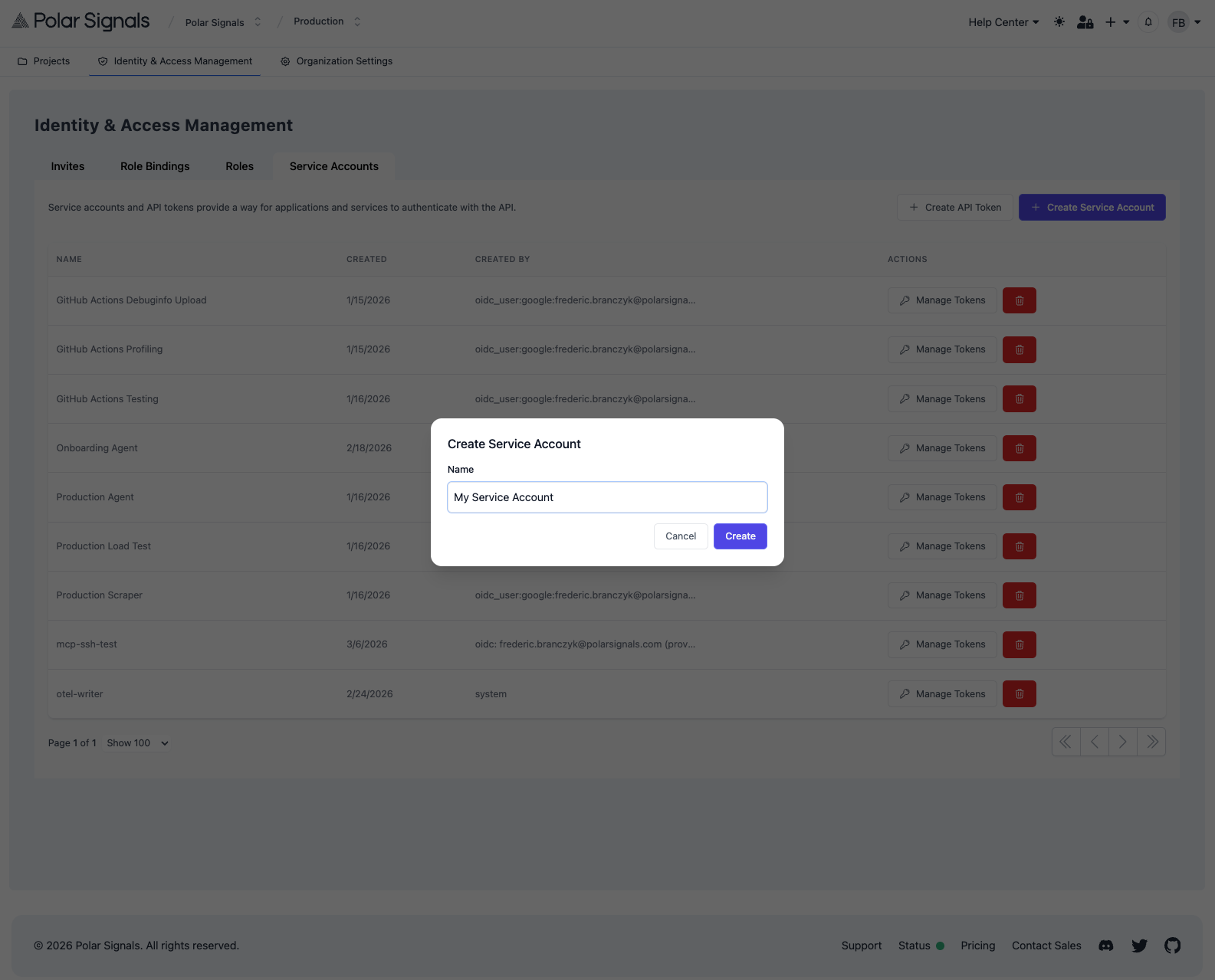
1. Create a Service Account
- Go to your organization settings
- Navigate to Identity & Access Management > Service Accounts
- Click Create Service Account
- Enter a descriptive name (e.g.,
ci-debuginfo-uploader)
2. Create a Role Binding
- Go to Identity & Access Management > Role Bindings
- Click Create Role Binding
- Select your new service account as the subject
- Select the Debug Info Writer role
- Optionally, scope the binding to a specific project
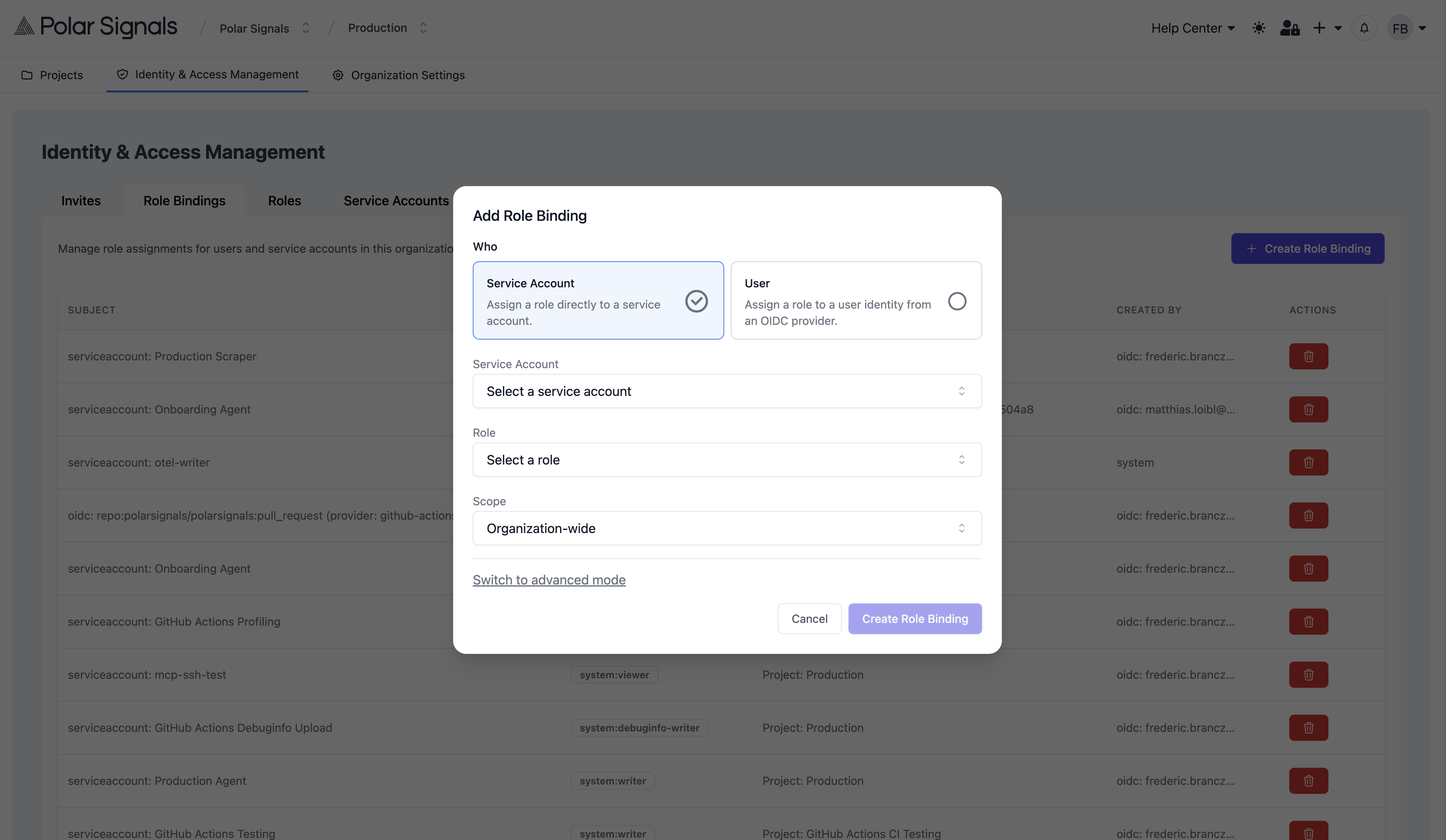
The Debug Info Writer role grants debuginfo.write, which covers both debuginfo and source uploads.
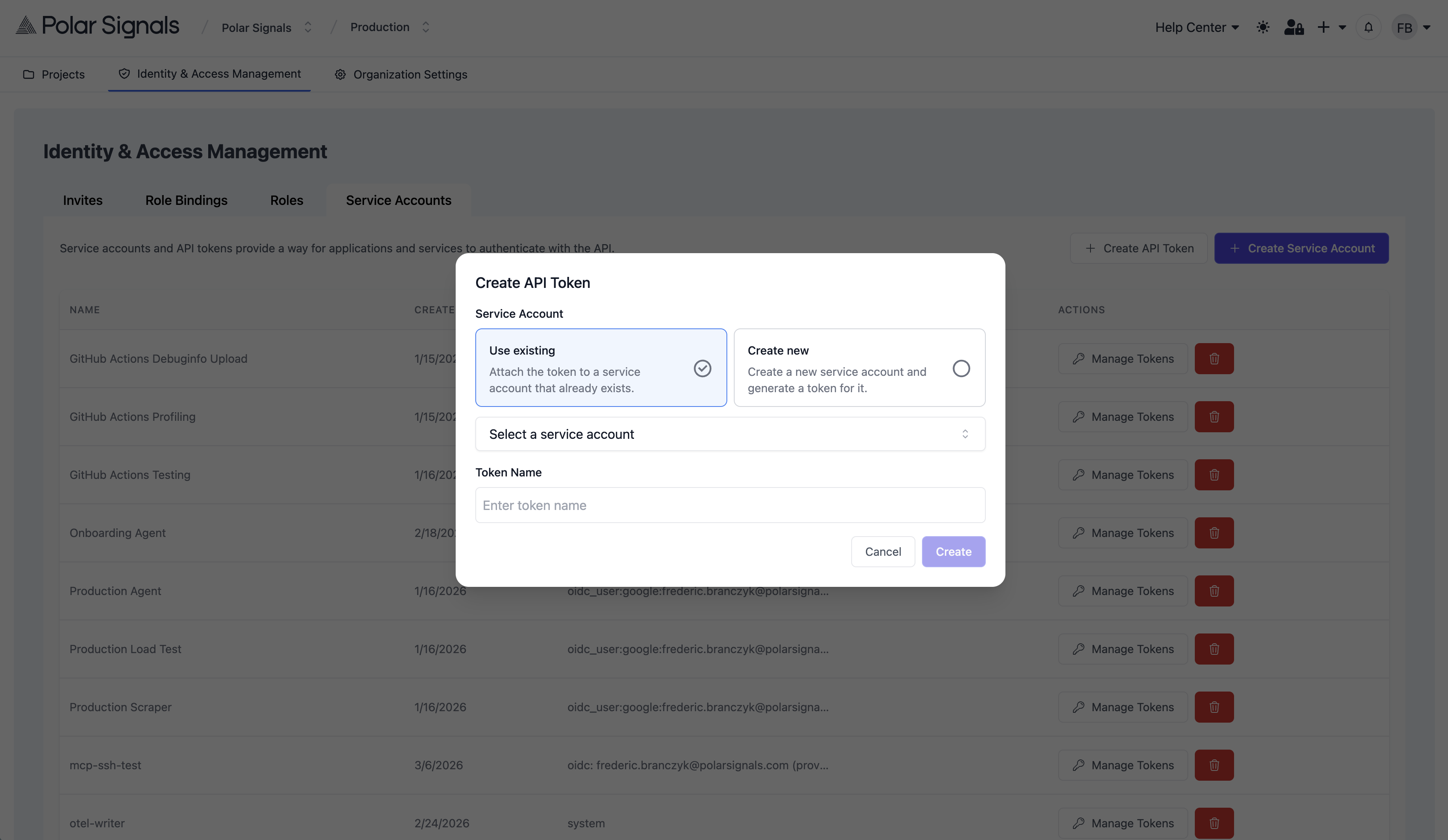
3. Generate a Token
- Go to Identity & Access Management > Service Accounts and click on the "Create API Token" button.
- You can either use an existing service account or create a new one specifically for the agent. If you create a new service account, make sure to assign it the appropriate role bindings as described in Step 2.
- Enter a descriptive name for the token
- Click Create Token
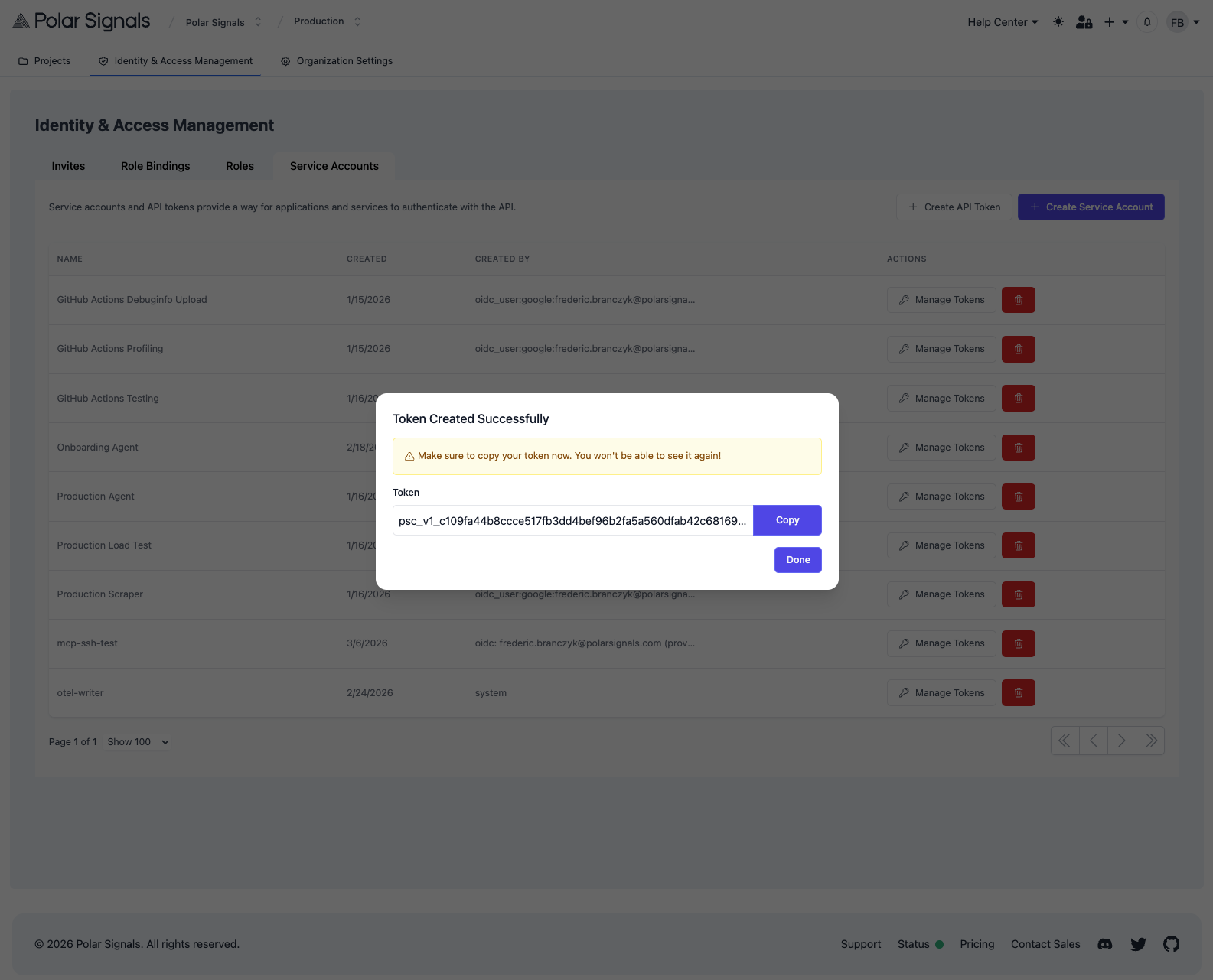
- Copy the token immediately — it is only shown once
4. Store the Token in Your CI System
Store the new service account token and project ID as secrets in your CI platform (e.g., GitHub Actions secrets, GitLab CI variables, etc.).
5. Update Your Upload Commands
Replace the old token with the new service account token and add the projectID header. The two key flags are:
- Token:
--bearer-token - Project ID:
--grpc-headers=projectID=<your-project-id>
For example:
parca-debuginfo upload \
--store-address=grpc.polarsignals.com:443 \
--bearer-token=$POLARSIGNALS_TOKEN \
--grpc-headers=projectID=$POLARSIGNALS_PROJECT_ID \
/path/to/your/binary
Find your project ID in your project settings in the Polar Signals Cloud UI.
6. Verify and Revoke
Run your CI pipeline and verify the upload succeeds. Then revoke the old project token to complete the migration.
See Also
- Generating Tokens — creating service accounts and tokens
- IAM — roles, permissions, and role bindings reference
- Uploading Debuginfos — debuginfo upload reference
- Upload Source — source upload reference